Tailscale made mesh VPNs mainstream. Install the app, sign in, and your devices see each other across any network. No port forwarding, no config files, no VPN server to maintain. It earned its reputation.
But Tailscale has trade-offs that matter to IT professionals. The control plane is proprietary and hosted on Tailscale’s infrastructure — you can’t self-host it, you can’t audit it, and your network metadata lives on someone else’s servers. The free tier is limited to personal use. Commercial pricing starts at $6/user/month. And you’re locked into a vendor whose source-available license restricts what you can do with the code.
If any of that bothers you, the good news is that 2026 has excellent alternatives. Several open-source projects now match or exceed Tailscale’s functionality while giving you full control over your infrastructure.
Here’s what’s worth your time.
Quick Comparison
| Tool | Type | Self-Hostable | License | Free Tier | Best For |
|---|---|---|---|---|---|
| NetBird | Mesh + Zero-Trust | Yes (full) | BSD-3 | 5 users, 100 machines | IT teams, SMBs, MSPs |
| Headscale | Mesh (Tailscale-compatible) | Yes | BSD-3 | Unlimited | Existing Tailscale users |
| Pangolin | Reverse proxy + VPN | Yes | Apache 2.0 | Unlimited | Exposing web apps securely |
| ZeroTier | Mesh (L2/L3) | Partial (controller) | BSL 1.1 | 25 devices | IoT, LAN gaming, multicast |
| Netmaker | Mesh | Yes (Community) | SSPL | 3 networks, 50 hosts | Complex multi-site networks |
| Firezone | Gateway + Zero-Trust | Yes | Apache 2.0 | Self-hosted free | Team access with SSO |
| Nebula | Mesh | Yes | MIT | Unlimited | Large-scale infrastructure |
1. NetBird — Best Overall Alternative
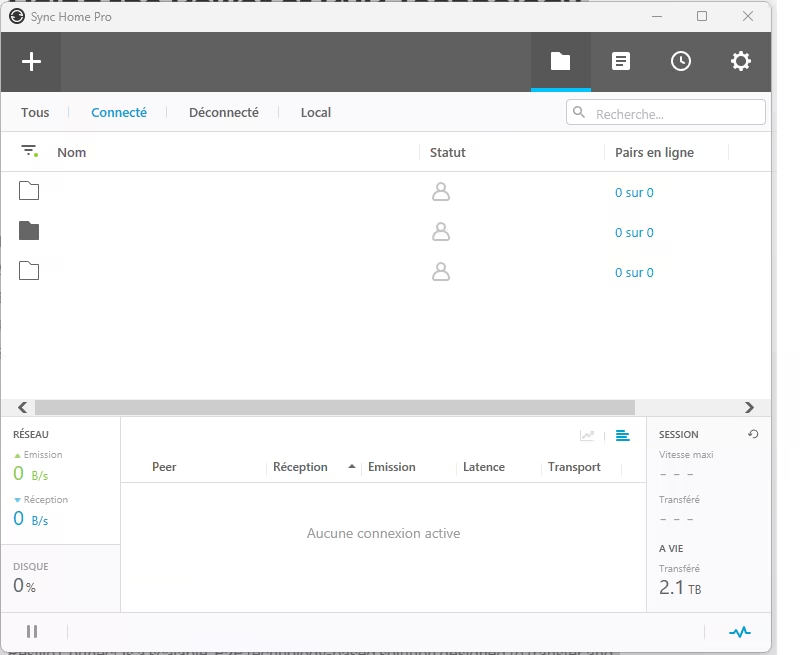
NetBird is the closest thing to “Tailscale, but you own everything.” It’s a WireGuard-based mesh VPN with zero-trust access controls, and every component — management server, signal server, relay — can run on your infrastructure under a BSD-3 license.
Why it’s the top pick:
- Full self-hosting. Not partial, not “bring your own relay.” Every piece of the stack is self-hostable. Since v0.62, deployment takes 4-5 containers and about 1 GB RAM.
- Zero-trust built in. Access policies are identity-based, not just network-based. Define who can reach what, on which ports, based on user groups. Tailscale’s ACLs do something similar, but NetBird’s model is more intuitive for teams with varied access needs.
- The Control Center. A real-time visual map of your network — peers, groups, policies, connection status. It’s one of the best network management interfaces we’ve used.
- CLI and API. Full management plane access through the REST API and CLI. Script peer provisioning, policy updates, DNS changes — everything Tailscale’s admin console does, NetBird’s API can automate.
- SSH without key management. Identity-based SSH access, mapped to local OS users. No more maintaining
authorized_keysfiles across your fleet.
Free tier: 5 users, 100 machines on the managed cloud. Self-hosted: unlimited, free forever.
Trade-offs vs Tailscale: Smaller ecosystem, fewer third-party integrations. NetBird’s client support is broad but doesn’t cover every NAS or router firmware that Tailscale does. Tailscale’s MagicDNS feels slightly more polished.
For a head-to-head, see our detailed NetBird vs Tailscale comparison. For our full deployment experience, read our NetBird review.
2. Headscale — Best for Existing Tailscale Users
Headscale is an open-source reimplementation of Tailscale’s coordination server. It works with the official Tailscale clients, which means you can self-host your control plane without changing anything on your devices.
Why it’s great:
- Drop-in replacement. Point your Tailscale clients at your Headscale server instead of Tailscale’s cloud. Same clients, your coordination.
- Massive community. 24K+ GitHub stars. Active development and a growing contributor base.
- Feature parity (mostly). MagicDNS, ACLs, exit nodes, subnet routers — most features work. Some newer Tailscale features (Funnel, Tailnet Lock) may lag behind.
- Zero cost. No pricing tiers, no device limits. Your only cost is a VPS to run the coordination server.
Trade-offs: You’re still running Tailscale’s source-available clients, not truly open-source software. No built-in web UI (community options like Headscale-UI exist but aren’t official). You inherit Tailscale’s client-side limitations and license terms.
Best for: Teams already running Tailscale who want to migrate to self-hosting without touching every endpoint. The migration path is straightforward — swap the coordination URL, re-authenticate, done.
3. Pangolin — Best for Exposing Web Apps
Pangolin is the newer player that’s been gaining traction fast, especially in the home lab community. It started as a self-hosted alternative to Cloudflare Tunnels for reverse proxying, but has evolved into a full identity-aware remote access platform.
Why it’s interesting:
- Reverse proxy + VPN in one. Expose web applications through encrypted tunnels without port forwarding, and access private resources through a client. It recently added private resource access, turning it into something closer to a zero-trust network access platform.
- Browser-based access. Users can reach web apps through the browser without installing any client. That’s a significant advantage for quick access to internal tools.
- Identity-aware. Auth is baked in — users authenticate before accessing any resource. Granular controls per resource and per user.
- Simple architecture. Hub-and-spoke model. Install the “Newt” client on your server, and it tunnels outbound to your Pangolin server. No complex mesh coordination needed.
Trade-offs: Not a true mesh VPN — it’s hub-and-spoke, so peers don’t talk directly. Newer project with a smaller community. Better suited for exposing specific services than building a full mesh network.
Best for: Self-hosters who want to expose internal web applications securely without Cloudflare dependencies. A great complement to a mesh VPN rather than a replacement. If you’re currently using Cloudflare Tunnels, Pangolin gives you the same capability without the third-party dependency.
4. ZeroTier — Best for Layer 2 Networking
ZeroTier takes a different approach from everything else on this list. While the others are Layer 3 (IP routing), ZeroTier operates at Layer 2 — it creates virtual Ethernet networks. Your devices act like they’re on the same LAN, including support for multicast, mDNS, and broadcast traffic.
Why it matters:
- True LAN emulation. Multicast and mDNS work out of the box. Services that rely on local network discovery (Chromecast, AirPlay, some IoT devices) work across ZeroTier without special configuration.
- VLAN-like segmentation. Create multiple virtual networks with different rules, similar to VLANs but over the internet.
- Mature and battle-tested. ZeroTier has been around since 2014. The network controller is self-hostable (though the default is cloud-hosted).
Trade-offs: Uses a custom protocol instead of WireGuard (no kernel-space speed advantage on Linux). Free tier is limited to 25 devices (vs 100 for Tailscale and NetBird). The self-hosted controller works but isn’t as polished as NetBird’s management server. BSL 1.1 license — open source after four years, but not truly open source today.
Best for: Environments where Layer 2 features matter: IoT networks, LAN gaming over the internet, service discovery across sites, or anything that needs multicast.
5. Netmaker — Best for Complex Topologies
Netmaker offers the most control over your WireGuard mesh topology. If you need egress gateways, relay nodes, custom routing tables, and fine-grained network segmentation, Netmaker gives you the levers.
Why it’s worth considering:
- Advanced routing. Egress gateways route traffic to external networks. Relay nodes help peers behind restrictive NAT. Custom DNS per network.
- Visual dashboard. Graph-based view of your network topology with connection status.
- Multi-tenant support. Multiple isolated networks from a single management plane.
Trade-offs: Steeper learning curve than NetBird or Headscale. Community Edition uses SSPL license (not OSI-approved open source). More complex deployment and ongoing maintenance. The project has had some turbulent periods in terms of governance and direction.
Best for: Enterprise or MSP environments with complex multi-site routing requirements that simpler mesh VPNs can’t handle.
6. Firezone — Best for SSO-First Teams
Firezone bridges the gap between a traditional VPN gateway and a zero-trust access platform. WireGuard-based, with strong SSO integration, audit logging, and DNS-based resource policies.
Why it fits:
- SSO integration. OIDC and SAML support (Google Workspace, Okta, Azure AD, Keycloak). Authentication is a first-class feature, not an add-on.
- Split tunneling. Route only specific traffic through the VPN. Access internal DNS names without routing all internet traffic.
- Audit logging. Who accessed what, when. Built for compliance-minded teams.
Trade-offs: Not a true peer-to-peer mesh — traffic routes through gateway nodes. Underwent significant architecture changes recently, which may affect existing deployments. Smaller community than NetBird or Headscale.
Best for: Teams whose primary need is secure, identity-based access to specific internal resources rather than full mesh networking between all devices.
7. Nebula — Best for Large-Scale Infrastructure
Nebula was built by Slack to connect their infrastructure. It’s a certificate-based overlay network designed for environments with thousands of nodes. MIT-licensed, proven at scale.
Why it exists:
- Certificate-based auth. Instead of API keys or SSO, Nebula uses a certificate authority model. You sign certificates for each node. No central coordination server needed after initial setup.
- Built-in firewall. Per-host firewall rules defined in the configuration.
- Proven scale. Originally built to connect Slack’s global infrastructure. It handles large deployments without breaking a sweat.
Trade-offs: No web UI. No user-friendly management console. Configuration is YAML files and certificate management. Not ideal for teams that want a dashboard and quick onboarding. Uses its own protocol (not WireGuard).
Best for: DevOps and infrastructure teams running large-scale distributed systems where certificate-based authentication and minimal dependencies matter more than user-friendliness.
How to Choose
If you’re coming from Tailscale and want the closest experience with self-hosting, Headscale is the path of least resistance.
If you want the best all-around alternative that combines mesh networking, zero-trust, and a great interface, NetBird is the one to beat.
If you need to expose web applications securely without Cloudflare, Pangolin fills that niche.
If Layer 2 networking and multicast matter, ZeroTier is your only real option.
If you have complex multi-site routing needs, Netmaker gives you the most control.
If SSO-based access to specific resources is your primary use case, Firezone does it well.
If you’re building infrastructure at massive scale, Nebula is battle-proven.
For a deeper dive into the full self-hosted VPN landscape (including traditional client-server options like WG-Easy and OpenVPN), see our complete guide to the best self-hosted VPN solutions in 2026.