The VPN landscape has shifted under our feet. Traditional client-server tunnels — the kind where you spin up an OpenVPN box and hand out config files — still work, but they feel like managing floppy disks in a cloud-first world. Meanwhile, mesh VPNs and zero-trust overlays have matured to the point where your devices find each other, negotiate encrypted tunnels, and enforce access policies without you babysitting a central gateway.
If you’re an IT pro, sysadmin, or MSP owner evaluating your options, the question isn’t just “which VPN software?” anymore. It’s “which architecture?” The answer depends on whether you’re connecting a home lab, securing a 30-person company’s access to internal file servers, or managing client networks across multiple sites.
We’ve deployed several of these tools in real environments. Here’s what actually works in 2026, organized by how the tools think about networking — not by marketing claims.
Why Self-Host Your VPN in 2026?
Before diving into tools, let’s address the obvious: why bother self-hosting when services like NordVPN and Surfshark exist?
Because those are consumer VPNs. They’re designed to mask your IP while streaming Netflix. That’s not what IT teams need. What you need is secure access to internal resources — file servers, databases, admin panels, monitoring dashboards — without exposing them to the public internet.
Self-hosting gives you:
- Full control over data and logs. You decide what gets logged. In regulated industries, this isn’t optional.
- No per-seat licensing. Commercial VPN platforms charge $5-15/user/month. With a 30-person team, that’s $1,800-5,400/year for something you can run on a $10/month VPS.
- No vendor lock-in. Your network topology shouldn’t depend on a startup’s Series B funding.
- Performance you control. Your server, your location, your bandwidth. No shared infrastructure throttling your throughput.
The trade-off is real: you own the maintenance. But in 2026, the best self-hosted VPN tools have made that maintenance remarkably light.
Understanding VPN Architectures: Traditional vs Mesh vs Zero-Trust
This is where most “best VPN” articles fail. They list 10 tools without explaining that these tools work in fundamentally different ways. Picking the wrong architecture is a bigger mistake than picking the wrong tool.
Traditional Client-Server VPN (Hub-and-Spoke)
This is the model you know. One server sits at the center. Every client connects to it. All traffic routes through that server.
How it works: You install a VPN server (WireGuard, OpenVPN) on a machine with a public IP. Clients connect to that IP, get assigned a tunnel IP, and route traffic through the server to reach internal resources.
When it fits:
- Single office or data center with remote workers connecting in
- Personal VPN for securing traffic on public Wi-Fi
- Simple setups where one tunnel endpoint is enough
Limitations: Every packet goes through the central server, even if two clients are on the same LAN. That server is a single point of failure and a bandwidth bottleneck. Scaling means scaling that one box.
Mesh VPN (Peer-to-Peer)
Mesh VPNs flip the model. Instead of routing everything through a central server, devices connect directly to each other. The “server” component only handles coordination — exchanging public keys, helping peers find each other through NAT — but actual traffic flows peer-to-peer.
How it works: Each device runs a lightweight agent. A coordination server (sometimes called a control plane) tells devices about each other. Devices then establish direct WireGuard tunnels between themselves. If a direct connection isn’t possible (restrictive NAT, corporate firewalls), traffic falls back to relay servers.
When it fits:
- Distributed teams across multiple locations
- Multi-site office connectivity
- Home lab access from anywhere
- Any scenario where devices need to talk to each other, not just to a central server
Why it matters: A sysadmin in Paris connecting to a file server in the same building doesn’t route through a VPN server in Frankfurt. The connection stays local, direct, and fast.
Zero-Trust Overlay Networks
Zero-trust takes mesh networking a step further. Instead of “you’re on the VPN, so you can access everything,” zero-trust means “prove who you are and what you’re allowed to access — every time.”
How it works: Identity-based access controls replace network-based ones. Your VPN client authenticates against an identity provider (SSO/OIDC). Access policies define which users or groups can reach which resources, on which ports. Being “on the network” doesn’t grant access to anything by default.
When it fits:
- Any organization that cares about security (so, everyone)
- Compliance requirements (SOC 2, ISO 27001)
- Teams with contractors, vendors, or rotating access needs
- Multi-site environments where flat network access is dangerous
The good news: in 2026, the best mesh VPN tools have zero-trust built in. You don’t have to choose between mesh and zero-trust — tools like NetBird give you both in one platform.
The Best Self-Hosted VPN Tools Compared
Here’s the overview before we go deep on each tool:
| Tool | Protocol | Architecture | Fully Self-Hostable | License | Free Tier | Best For |
|---|---|---|---|---|---|---|
| NetBird | WireGuard | Mesh + Zero-Trust | Yes (all components) | BSD-3 | 5 users, 100 machines | IT teams, SMBs, MSPs |
| Headscale | WireGuard | Mesh | Yes | BSD-3 | Unlimited (self-hosted) | Tailscale users wanting self-hosting |
| WG-Easy | WireGuard | Client-Server | Yes | Custom | Unlimited | Personal use, simple tunnels |
| Firezone | WireGuard | Gateway + Zero-Trust | Yes | Apache 2.0 | Self-hosted free | Team access management |
| Netmaker | WireGuard | Mesh | Yes (Community) | SSPL | 3 networks, 50 hosts | Complex multi-site networks |
| OpenVPN AS | OpenVPN | Client-Server | Yes | Proprietary | 2 connections | Legacy compatibility |
NetBird — Best Overall for IT Teams
NetBird is the tool we keep coming back to. It combines a WireGuard-based mesh VPN with zero-trust access controls in a single, open-source platform — and every component can run on your own infrastructure.
What makes it stand out isn’t any single feature. It’s how everything fits together. The web dashboard (they call it the Control Center) gives you a real-time visualization of your entire network: which peers are connected, which access policies apply, which groups have access to what. For a sysadmin managing 20-50 endpoints, this kind of visibility is invaluable.
Why we’re fans:
- The UX is seamless. Install the agent, authenticate, and you’re on the network. We’ve onboarded non-technical users in under two minutes. The interface is clean, intuitive, and you can tell it was designed for daily use rather than as an afterthought.
- SSH without key management. NetBird handles SSH access with identity-based controls. No more distributing SSH keys or maintaining
authorized_keysfiles across your fleet. You define who can SSH into which machines based on their identity, and NetBird handles the rest. - Access policies that make sense. Define which user groups can reach which resources, on which ports. A developer doesn’t need access to the database admin panel. A contractor doesn’t need to see the internal wiki. Zero-trust isn’t a buzzword here — it’s how the tool actually works.
- The CLI and API are genuinely powerful. This is what sealed it for us. Managing peers, routes, policies, and DNS through the CLI or REST API means you can script your entire network configuration. Provision new sites, update policies, rotate access — all programmatically. For IT pros who live in the terminal, this elevates NetBird from “nice VPN” to “network infrastructure tool.”
- Reverse proxy (new). NetBird recently added a reverse proxy feature, opening up use cases that previously required tools like Cloudflare Tunnels. We haven’t tested it in depth yet, but the direction is promising.
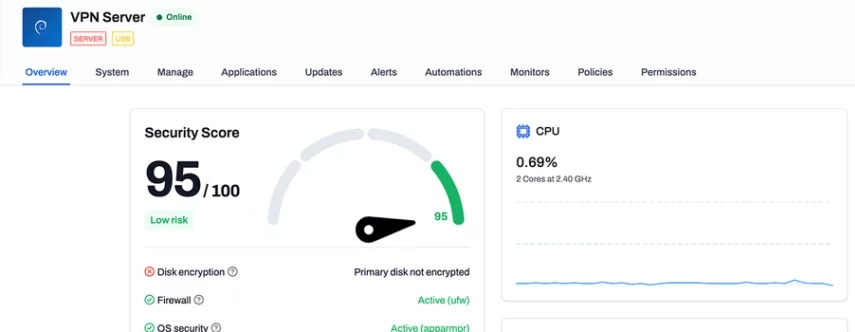
Self-hosting: Every component — management server, signal server, relay (TURN) — runs on your infrastructure. Since v0.62, setup has become significantly easier: fewer containers (4-5 vs 7+ previously), lower resource requirements (~1 GB RAM), and built-in local user management. BSD-3 license means no open-core surprises.
Free cloud tier: If you don’t want to self-host, the managed cloud version gives you 5 users and 100 machines at no cost. That’s generous enough for most small teams.
For a deeper look at our experience, check out our hands-on NetBird review.
Headscale — Best Tailscale-Compatible Self-Hosted Option
If you’re already using Tailscale and love the client experience but want to own your control plane, Headscale is the answer. It’s an open-source reimplementation of Tailscale’s coordination server, and it works with the official Tailscale clients.
What it does well:
- Drop-in replacement for Tailscale’s cloud coordination
- Works with official Tailscale clients on every platform (Windows, macOS, Linux, iOS, Android)
- 24K+ GitHub stars and active development
- MagicDNS, ACL support, exit nodes — most Tailscale features work
Limitations:
- You’re still dependent on Tailscale’s clients, which are source-available but not fully open source
- Some Tailscale features (Funnel, Tailnet Lock) may not be supported
- No web UI out of the box (though community projects like Headscale-UI exist)
When to choose Headscale over NetBird: If your team already uses Tailscale clients and you want a migration path to self-hosting without redeploying agents on every machine.
WG-Easy — The Simplest WireGuard Server
WG-Easy is exactly what it sounds like: WireGuard made easy. It’s a single Docker container that gives you a WireGuard server with a clean web UI for managing peers.
docker run -d \
--name wg-easy \
-e WG_HOST=your. server.ip \
-e PASSWORD=your-admin-password \
-v ~/.wg-easy:/etc/wireguard \
-p 51820:51820/udp \
-p 51821:51821/tcp \
--cap-add=NET_ADMIN \
--cap-add=SYS_MODULE \
ghcr.io/wg-easy/wg-easyThat’s it. You have a VPN server. Generate client configs from the web UI, scan the QR code on your phone, done.
When to use it: Personal VPN, home lab remote access, or any scenario where you need one tunnel endpoint and don’t need mesh networking or access policies. It’s the right tool when your requirements are genuinely simple.
When to skip it: Multiple sites, team access management, identity-based policies — that’s mesh VPN territory.
Firezone — Best for Team Access Management
Firezone sits between a traditional VPN gateway and a full mesh network. It’s WireGuard-based with built-in SSO integration, audit logging, and access policies. Think of it as “OpenVPN Access Server, but modern and actually pleasant to use.”
What it does well:
- Clean admin panel for managing users and policies
- OIDC/SAML authentication (Google Workspace, Okta, Azure AD)
- Split tunneling and DNS-based resource access
- Audit logs for compliance
Limitations:
- Not a true mesh — traffic routes through gateway nodes
- Smaller community than NetBird or Headscale
- Recent architecture changes may affect existing deployments
When to choose it: Teams that need gateway-style VPN access with modern identity integration, especially if your use case doesn’t require peer-to-peer mesh.
Netmaker — Best for Complex Network Topologies
Netmaker gives you the most control over your WireGuard mesh topology. Egress gateways, relay nodes, custom DNS, and fine-grained ACLs — it’s powerful but demands more from you in return.
What it does well:
- Full WireGuard mesh with advanced routing capabilities
- Egress gateways for routing traffic to external networks
- Relay nodes for peers behind restrictive NAT
- Dashboard for visual network management
Limitations:
- Steeper learning curve than NetBird or Headscale
- Community Edition is SSPL-licensed (not truly open source)
- More complex deployment and maintenance
When to choose it: Multi-site enterprise environments with complex routing requirements where you need granular control over network topology.
OpenVPN Access Server — The Legacy Standard
OpenVPN has been around for over two decades. It’s not the fastest (WireGuard outperforms it 3-5x in most benchmarks), and the codebase is orders of magnitude larger (~100,000+ lines vs WireGuard’s ~4,000). But it runs on virtually everything, supports every authentication method imaginable, and has the kind of battle-tested reliability that comes from 20 years in production.
When it still makes sense:
- Legacy devices that don’t support WireGuard
- Compliance requirements that specifically mandate OpenVPN
- Environments where you need to tunnel over TCP port 443 to bypass restrictive firewalls (WireGuard is UDP-only)
Self-hosting: OpenVPN Access Server is free for up to two simultaneous connections. Beyond that, you need a subscription. The community edition (without Access Server) is fully open source.
For most new deployments in 2026, WireGuard-based tools are the better choice. But if you have a specific reason to need OpenVPN, it’s still a solid option. We cover the protocol differences in detail in our WireGuard vs OpenVPN comparison.
Which Self-Hosted VPN Is Right for You?
Architecture and tool selection should follow your use case, not the other way around. Here’s how to choose:
Home Lab / Personal Use
Recommendation: WG-Easy or Headscale
If you need to access your home lab from a coffee shop or a hotel, WG-Easy gives you a working VPN in five minutes. If you want your laptop, phone, and NAS to all see each other regardless of location, Headscale (with Tailscale clients) or NetBird makes more sense.
Don’t overthink it for personal use. WG-Easy is the 90% solution.
Small to Medium Business (5-50 People)
Recommendation: NetBird
This is where NetBird pulls ahead. Your team needs to reach shared file servers, internal applications, and admin panels — without those resources being exposed to the internet. NetBird’s zero-trust policies mean the new hire gets access to exactly what they need, and nothing more. When someone leaves, revoke their identity and they’re off the network instantly.
The software works smoothly. The use cases are broad — from connecting branch offices to giving remote workers secure access to internal tools. And the Control Center gives you the kind of visibility that used to require expensive commercial solutions.
If you integrate NetBird with an identity provider like Zitadel or Keycloak, you get SSO-based access across your entire network.
MSP / Multi-Tenant Environments
Recommendation: NetBird (with API automation)
MSPs need isolation between client networks and the ability to provision and tear down environments programmatically. NetBird’s API makes this practical — script your client onboarding, define per-client access policies, and manage everything from the CLI without clicking through a web UI for each client.
The alternative is Netmaker if you need complex routing between client sites, but NetBird’s API-first approach is a better fit for most MSP workflows.
Quick Comparison: WireGuard vs OpenVPN
Since most tools in this guide are built on WireGuard, here’s why:
| Factor | WireGuard | OpenVPN |
|---|---|---|
| Speed | 3-5x faster (kernel-space) | Slower (user-space) |
| Codebase | ~4,000 lines | ~100,000+ lines |
| Audit surface | Small, easy to audit | Large, complex |
| Protocol | UDP only | TCP and UDP |
| Compatibility | Linux, Windows, macOS, iOS, Android | Everything including legacy |
| NAT traversal | Needs helpers (STUN/TURN) | Built-in (TCP 443) |
WireGuard wins on speed, simplicity, and security. OpenVPN wins on compatibility and the ability to run over TCP (useful in restrictive networks, though not for circumvention — WireGuard traffic is easily fingerprinted by deep packet inspection).
For most self-hosted deployments in 2026, WireGuard is the right foundation.
Frequently Asked Questions
What Is the Best Self-Hosted VPN?
For IT teams and small businesses, NetBird offers the best combination of mesh networking, zero-trust security, and ease of use — all fully self-hostable under a BSD-3 license. For simple personal tunnels, WG-Easy is hard to beat. For Tailscale users wanting self-hosting, Headscale is the natural choice.
Can I Self-Host Tailscale?
Not officially. Tailscale’s control plane is proprietary. However, Headscale is an open-source reimplementation that works with official Tailscale clients. NetBird is the other alternative if you want a fully open-source mesh VPN built for self-hosting from the ground up.
What Is a Mesh VPN?
A mesh VPN creates direct, encrypted tunnels between devices instead of routing all traffic through a central server. Each device connects peer-to-peer, with a lightweight coordination server only handling discovery and key exchange. This eliminates the central bottleneck and keeps traffic fast and local. Learn more in our mesh VPN guide.
Is WireGuard Better Than OpenVPN?
For most use cases, yes. WireGuard is 3-5x faster, has a vastly smaller codebase (~4,000 lines vs 100,000+), and uses modern cryptography. OpenVPN still has advantages in legacy compatibility and TCP support. We cover the details in our WireGuard vs OpenVPN comparison.
How Much Does a Self-Hosted VPN Cost?
The software is free. Your costs are infrastructure: a VPS ($5-20/month) or an existing server. NetBird’s cloud free tier (5 users, 100 machines) costs nothing. Even self-hosting the management plane requires minimal resources — about 1 GB RAM and 1 vCPU.
Conclusion
The self-hosted VPN landscape in 2026 is the best it’s ever been. WireGuard solved the protocol problem. Mesh networking solved the topology problem. Zero-trust solved the access control problem. And open-source projects like NetBird, Headscale, and WG-Easy have made all of it accessible to IT teams of any size.
If you’re deploying fresh today, start with the architecture that matches your needs. A home lab needs a simple tunnel. A business needs mesh networking with access policies. An MSP needs API-driven provisioning and client isolation.
For most IT professionals reading this, NetBird is the tool that checks the most boxes. The mesh networking works smoothly, the zero-trust policies are practical (not just theoretical), the CLI and API make automation genuinely easy, and the fact that it’s fully open source under BSD-3 means you’re never locked in.
Whatever you choose, stop routing your team’s traffic through a single OpenVPN box you set up in 2019. The tools have caught up to the architecture. It’s time your VPN did too.