If you manage more than a handful of computers, you have probably asked yourself: what is RMM, and why does every MSP swear by it? The short answer is that RMM software lets you monitor, manage, and fix endpoints remotely — without leaving your desk or interrupting the person sitting at that machine.
The longer answer is more interesting. RMM tools have evolved from simple ping-and-alert systems into full-blown IT management platforms. They handle patching, scripting, remote access, inventory, and automated remediation. Whether you run a 10-person internal IT team or an MSP managing 500 client endpoints, RMM is likely the single tool that will save you the most time.
In this guide, we will break down what RMM means, how it works under the hood, who actually needs one, and how to pick the right option without overspending. No vendor fluff — just a practical explanation for IT pros who want to understand the landscape.
What Does RMM Stand For?
RMM stands for Remote Monitoring and Management. That three-word phrase covers a lot of ground, so let’s unpack it:
- Remote — You manage devices over the network, not by walking to each desk. This works across the hall or across the globe.
- Monitoring — The software continuously watches system health: CPU, RAM, disk usage, service status, event logs, and more. When something goes sideways, you know immediately.
- Management — You can take action on those devices remotely. Run scripts, push patches, install software, restart services, or open a full remote desktop session.
The RMM meaning in practice is straightforward: it is the central nervous system for IT operations. Instead of reacting to user complaints, you see problems before they become tickets. Instead of remoting into machines one by one, you push changes to hundreds of endpoints at once.
You might also see the terms “remote monitoring and management explained” in vendor marketing, but the concept is the same regardless of who is selling it. RMM software gives IT teams visibility and control over every managed device from a single console.
What Can RMM Software Do?
RMM tools vary in scope, but most share a core set of features. Here is what you should expect from any serious RMM platform:
Real-Time Monitoring and Alerting
The foundation of any RMM. Agents installed on endpoints report health metrics back to a central server. You define thresholds — disk above 90%, a critical service stops running, an event log entry matches a pattern — and the system fires an alert. Good RMMs let you customize alert severity, route notifications to different teams, and auto-resolve known issues.
Remote Access
Most RMMs include built-in remote desktop or remote shell capabilities. This lets you troubleshoot a workstation without asking the user to install a separate tool. Some platforms use their own protocol; others integrate with tools like MeshCentral or RustDesk.
Patch Management
One of the biggest time sinks in IT is keeping systems patched. RMM software automates this by scanning endpoints for missing updates, scheduling patch windows, and reporting on compliance. The best tools handle Windows updates, third-party software (browsers, runtimes, productivity apps), and even Linux packages.
Scripting and Automation
Need to deploy a registry change to 200 machines? Push a PowerShell script from the console. RMMs let you run scripts on demand or on a schedule — PowerShell, Bash, Python, batch files, whatever the endpoint supports. This is where RMM transforms from a monitoring tool into a genuine automation platform.
Hardware and Software Inventory
RMMs collect detailed inventory data: installed software, hardware specs, warranty status, network configuration, logged-in users. This data feeds into reporting and compliance audits. When your CISO asks “how many machines are still running Windows 10?” — your RMM should answer that in seconds.
Endpoint Security Integration
Many RMMs now integrate with antivirus, EDR, and backup solutions. Some include their own security layers. At minimum, your RMM should tell you which machines have outdated antivirus definitions or disabled firewalls.
How Does RMM Work?
Remote monitoring and management explained at the architecture level is surprisingly simple. Most RMMs follow the same pattern:
The Agent
A lightweight software agent gets installed on every endpoint you want to manage. This agent runs as a background service, consuming minimal resources. It collects health data, executes tasks sent from the server, and maintains a persistent connection back to the console.
Agents are typically deployed via MSI/EXE installers, GPO, or scripted installs. Once running, the agent checks in with the server on a regular interval — usually every 30 to 120 seconds. Some platforms use a websocket connection for near-real-time communication.
The Server (Console)
The server is your command center. It can be cloud-hosted (SaaS) or self-hosted, depending on the platform. The server receives telemetry from all agents, processes alert rules, stores inventory data, and provides the web-based dashboard you interact with daily.
When you trigger a remote action — run a script, reboot a machine, open a remote session — the server relays that command to the target agent.
Alert Pipeline
The flow looks like this:
- Agent collects a metric (for example, disk usage hits 95%)
- Agent reports to the server
- Server evaluates the metric against your alert rules
- If a rule matches, the server fires a notification (email, Slack, webhook, SMS)
- Optionally, the server triggers an automated remediation (run a cleanup script, restart a service)
This pipeline runs continuously across every managed endpoint. The result is that problems surface before users even notice them.
Who Needs an RMM?
RMM software is not exclusive to massive enterprises. If any of the following sound familiar, you probably need one:
Managed Service Providers (MSPs)
MSPs are the classic RMM audience. When you manage IT for dozens of clients, you need a single pane of glass across all their environments. RMM platforms are built for multi-tenancy — you can segment clients, apply different policies per organization, and generate per-client reports.
Internal IT Teams
You don’t have to be an MSP to benefit. If your internal IT team manages more than 20-30 endpoints, manual management stops scaling. An RMM lets a team of two or three sysadmins manage hundreds of machines without heroics. Patch compliance alone justifies the investment.
Solo Sysadmins and Small Businesses
Even a one-person IT department gains massive leverage from RMM. Automated patching, proactive alerts, and remote access mean you spend less time firefighting and more time on projects that actually move the business forward.
Signs You Have Outgrown Manual Management
- You are remoting into machines one at a time to push updates
- You find out about outages from users, not your tools
- You have no reliable inventory of what is installed where
- Patch compliance is a spreadsheet you update manually
- You spend more time on repetitive tasks than strategic work
If you checked two or more of those boxes, it is time to look at RMM seriously.
RMM vs MDM vs ITSM: What’s the Difference?
These acronyms get thrown around together, but they solve different problems. Here is how they compare:
| RMM | MDM | ITSM | |
|---|---|---|---|
| Full name | Remote Monitoring and Management | Mobile Device Management | IT Service Management |
| Focus | Endpoints (desktops, servers, workstations) | Mobile devices (phones, tablets, laptops) | IT service delivery and support processes |
| Core job | Monitor health, automate tasks, remote access | Enforce policies, deploy apps, wipe devices | Ticketing, change management, SLA tracking |
| Examples | TacticalRMM, Datto, ConnectWise Automate | Intune, Jamf, Fleet | ServiceNow, Freshservice, Jira Service Management |
| Who uses it | MSPs, sysadmins, IT teams | IT teams managing mobile/BYOD fleets | IT support teams, service desks |
RMM vs Monitoring-Only Tools
You might also wonder how RMM compares to dedicated monitoring solutions like Zabbix, Nagios, or Prometheus. The key difference is the “Management” part. Monitoring tools watch and alert. RMM tools watch, alert, and act. You can push scripts, patches, and software from your RMM — something Zabbix was never designed to do.
That said, monitoring-only tools often offer deeper metric collection, custom dashboards, and better support for network devices (switches, firewalls, SNMP). Many IT teams run both: an RMM for endpoint management and a monitoring platform for infrastructure observability.
Free vs Paid RMM: What Are Your Options?
The RMM market used to be entirely pay-per-agent. That has changed. Today you have genuine free and open-source options alongside traditional commercial platforms.
Free and Open-Source RMMs
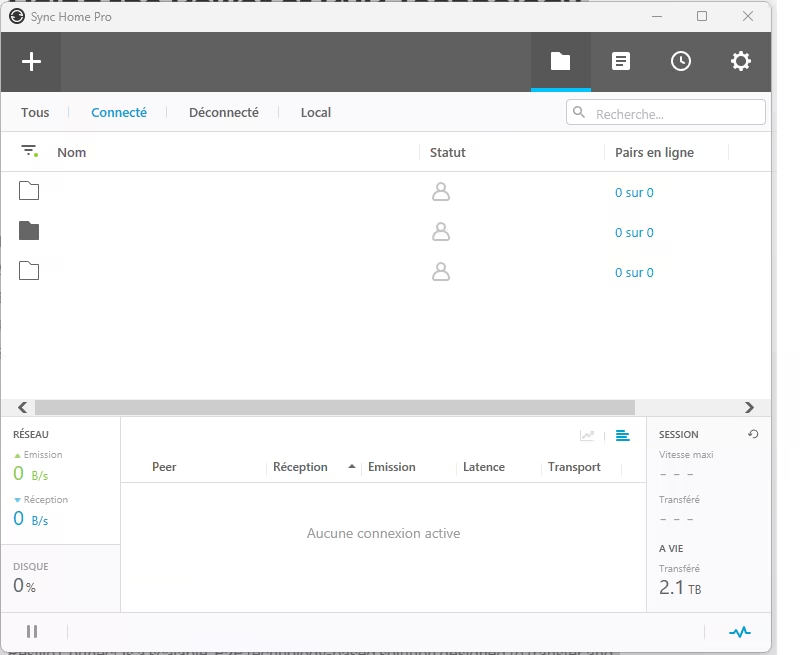
- TacticalRMM — A fully open-source, self-hosted RMM built on Django and Vue.js. It includes agents for Windows and Linux, remote scripting, patch management, and built-in remote access via MeshCentral. It is one of the most complete free RMMs available and has an active community.
- NetLock RMM — Another open-source RMM worth looking at. It takes a different architectural approach and is worth evaluating if TacticalRMM does not fit your workflow.
Free-Tier Commercial RMMs
- Action1 — A cloud-based patching and endpoint management platform with a generous free tier (up to 200 endpoints). It handles patch management, software deployment, and basic monitoring without requiring you to self-host anything.
Paid Commercial RMMs
Commercial options like Datto RMM, ConnectWise Automate, NinjaOne, and N-able offer polished interfaces, vendor support, deep integrations, and compliance features. They typically charge per agent per month ($2-$7 per endpoint is common). For MSPs managing thousands of endpoints with SLA requirements, the investment often makes sense.
How to Decide
The choice comes down to three factors:
- Budget — If you have zero software budget, start with TacticalRMM or Action1’s free tier. Both are production-ready.
- Scale — Managing 50 endpoints? A free tool works great. Managing 5,000 across multiple clients? Paid platforms offer better multi-tenancy and vendor support.
- Self-hosting appetite — Open-source RMMs require you to maintain the server infrastructure. If you prefer SaaS, lean toward cloud-based options.
For a detailed comparison of free options, check out our guide to the best free RMM tools.
Getting Started with RMM
If you have read this far and decided you need an RMM, here is a practical path to getting started:
1. Define your scope. How many endpoints? What operating systems? Do you need multi-tenancy for different clients or departments?
2. Pick a platform. For most small IT teams, we recommend starting with TacticalRMM (if you are comfortable self-hosting) or Action1 (if you want cloud-based simplicity). Both let you start free and scale up.
3. Deploy agents to a test group. Do not roll out to every machine on day one. Start with 5-10 endpoints, configure your alert policies, and learn the platform’s workflow.
4. Set up your core automations. Patch management schedules, disk space alerts, service monitoring for critical applications. These three alone will save hours per week.
5. Expand gradually. Once you trust your policies, roll agents out to the rest of your fleet. Refine alert thresholds to reduce noise, build script libraries for common tasks, and start using inventory reports for compliance.
The biggest mistake IT teams make with RMM is overcomplicating the initial setup. Start with the basics — monitoring, patching, remote access — and layer on automation as you get comfortable. A well-configured RMM with three solid alert policies beats a complex setup that nobody trusts.
RMM is not a luxury reserved for big MSPs. It is a fundamental tool for any IT team that wants to move from reactive firefighting to proactive management. The sooner you deploy one, the sooner you stop learning about problems from frustrated users and start fixing them before anyone notices.